Landfall Spyware Exploited Samsung Galaxy Phones in Middle East, Researchers Say

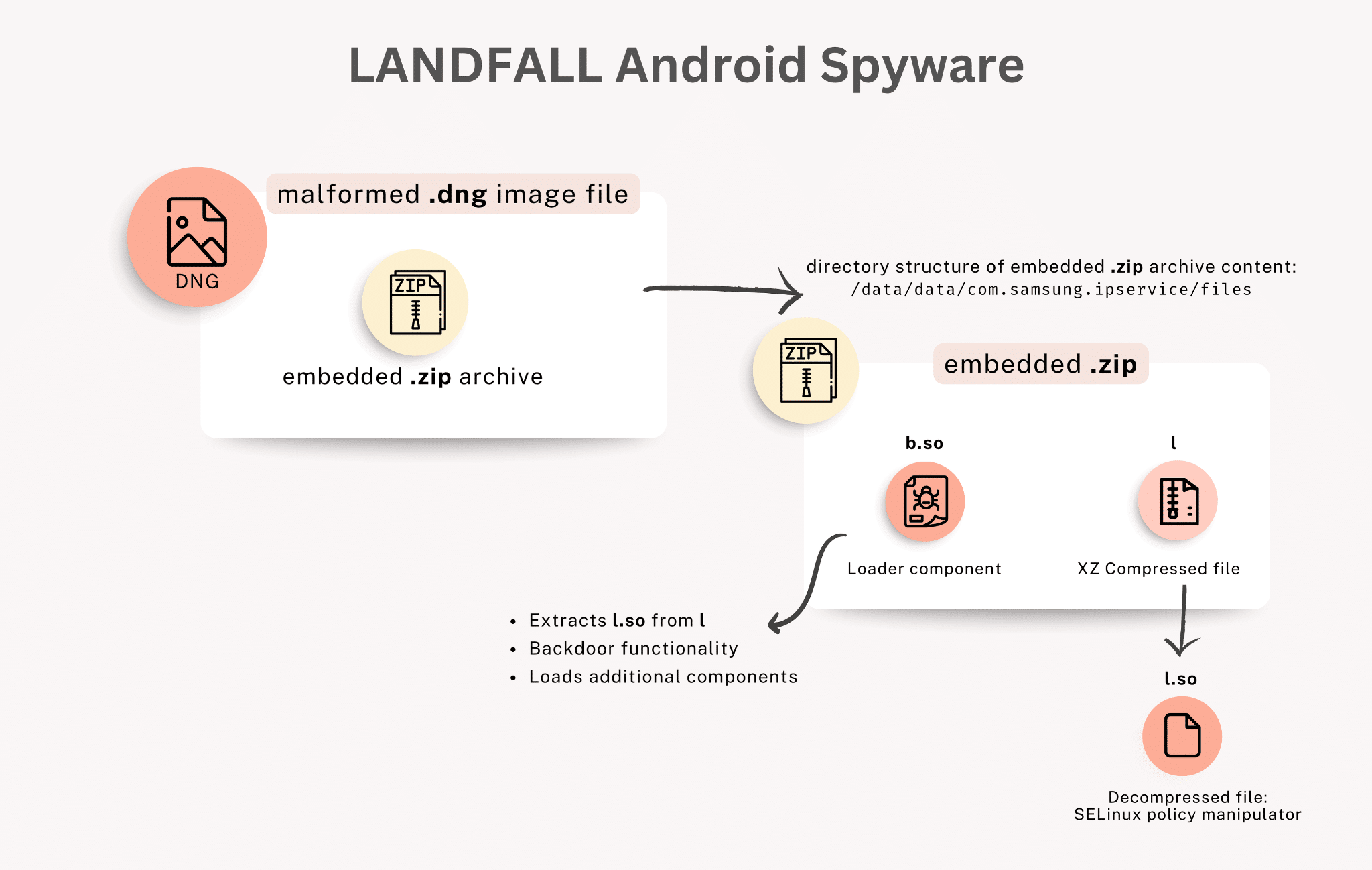
A newly discovered spyware campaign quietly targeted Samsung Galaxy smartphones through a now-fixed software flaw. Security researchers at Palo Alto Networks’ Unit 42 say the spyware, called Landfall, used a zero-day vulnerability. It let attackers compromise devices just by sending a specially crafted image.
Thankfully, the April 2025 security update fixed actively exploited “Landfall” vulnerability
The bug, tracked as CVE-2025-21042, was found in Samsung’s image-processing library. It was patched in the April 2025 security update. That’s another reason to keep your Galaxy device up to date with the latest patches. Researchers say the attack used Digital Negative (DNG) image files disguised as regular JPEGs and shared through WhatsApp. When one of these images reached a Galaxy phone, the exploit ran automatically.
Credits: Unit 42
Once active, Landfall could access stored data such as messages, photos, and contacts. It could also record audio and track location. The spyware’s code mentioned several models, including the Galaxy S22, S23, S24, and select Z Fold and Z Flip devices running Android 13 through 15.
The research firm claims it notified Samsung long before they patched it
Unit 42 says it first detected signs of the operation in July 2024. The group claims it privately notified Samsung later that year, but the company released a patch several months afterward. Researchers noted that the campaign was not widespread and instead targeted a small group of individuals.
Samples of the spyware were uploaded to VirusTotal from Turkey, Iran, Iraq, and Morocco, suggesting most activity occurred in the Middle East. Turkey’s national cybersecurity team also flagged one of the command-and-control servers linked to the campaign as malicious.
Unit 42 found some overlap between Landfall’s infrastructure and systems previously tied to Stealth Falcon, a surveillance group known for earlier espionage campaigns in the region. However, there isn’t enough evidence to determine who developed or deployed the spyware.